Hello @Apurva Pathak,
Hope you're doing well! Thanks for the update.
I tested this in my lab by creating the storage account and private endpoint in East US and running the test from West US 2, and it worked fine. I’ve attached a screenshot with my results. Please check if both your working and failing VMs return the same output.
Please follow the steps below for the Client VM.
1.Please verify the DNS resolution, it should resolve to the Private Endpoint’s private IP of your resource.
nslookup storage account .file.core.windows.net
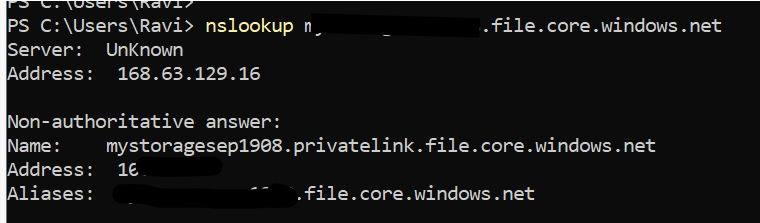
- If the DNS resolves correctly but
TCPTestSucceeded fails, then the issue is likely related to routing or peering.
Test-NetConnection storage account.file.core.windows.net -Port 445
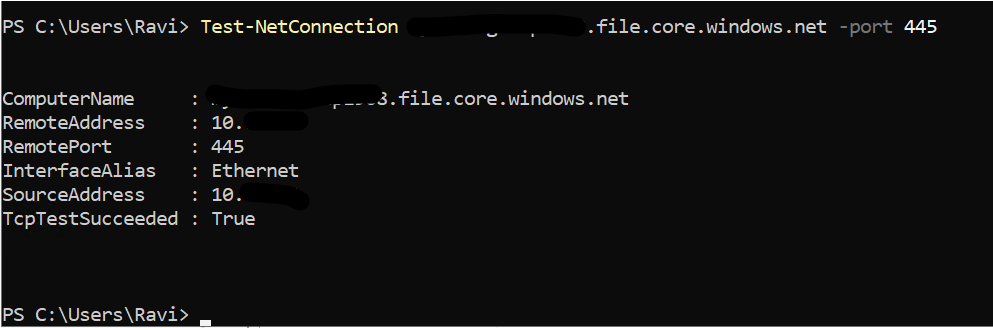
3.Please check the effective routes on the NIC and confirm that a route to 10.x.x.0 (PE private IP) exists via VirtualNetwork. In my screenshot, it shows as an interface endpoint because I didn’t create the VM in the same region as the Private Endpoint. Since you have VMs on both sides, the route should appear via VirtualNetwork in your case.
az network nic show-effective-route-table \ --name <CLIENT_VM_NIC_NAME> \ --resource-group <CLIENT_RG> \ -o table
Run the following command on both VMs (Client VNet and PE VNet):
az network vnet peering list --resource-group <RG_NAME> --vnet-name <VNET_NAME> -o table
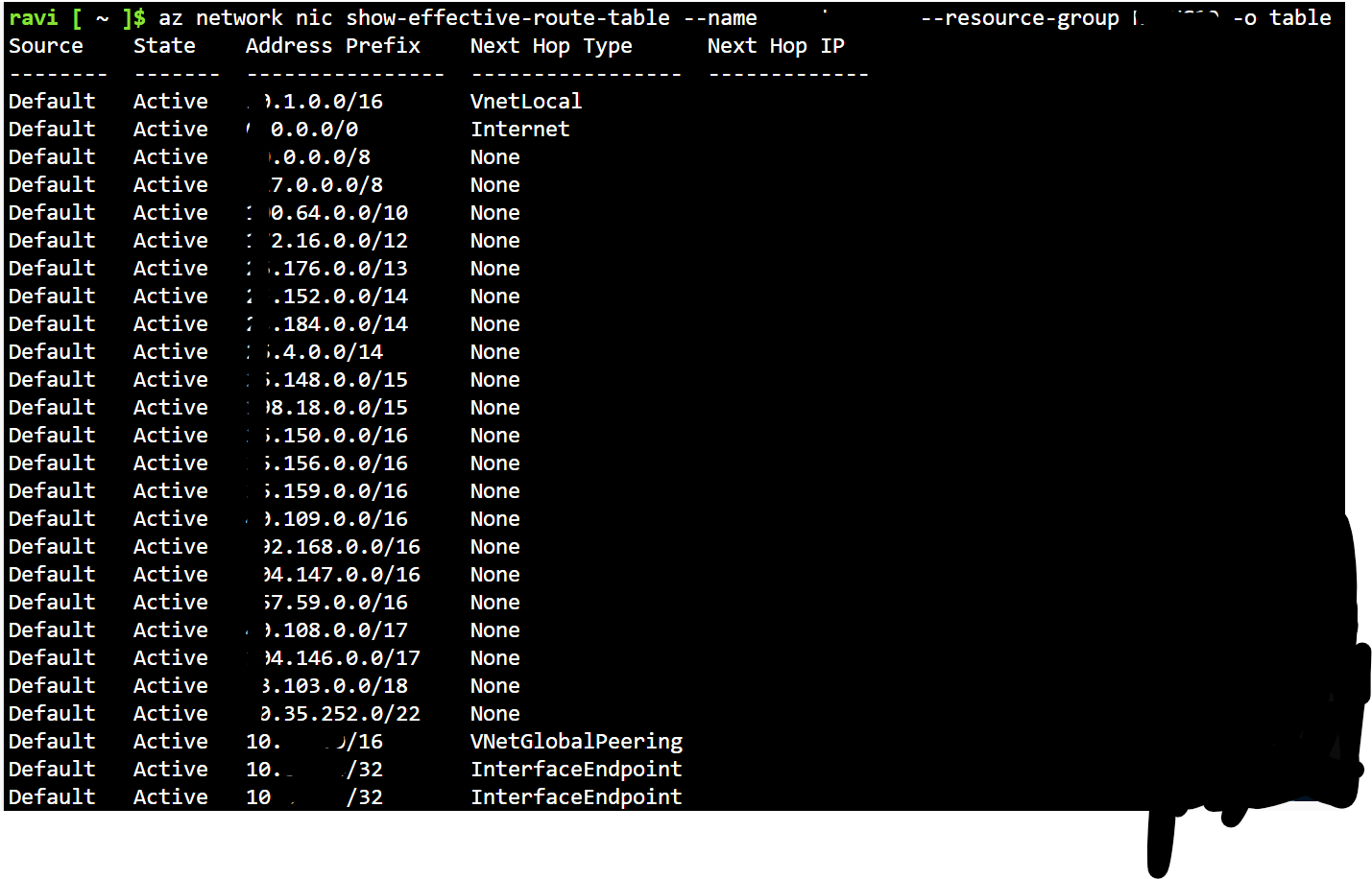
Make sure the settings are as follows:
-
"allowVirtualNetworkAccess": true
-
"allowForwardedTraffic": true (required if there’s a UDR or firewall in the path)
Traffic must be enabled in both directions. Please refer to the screenshot below for guidance
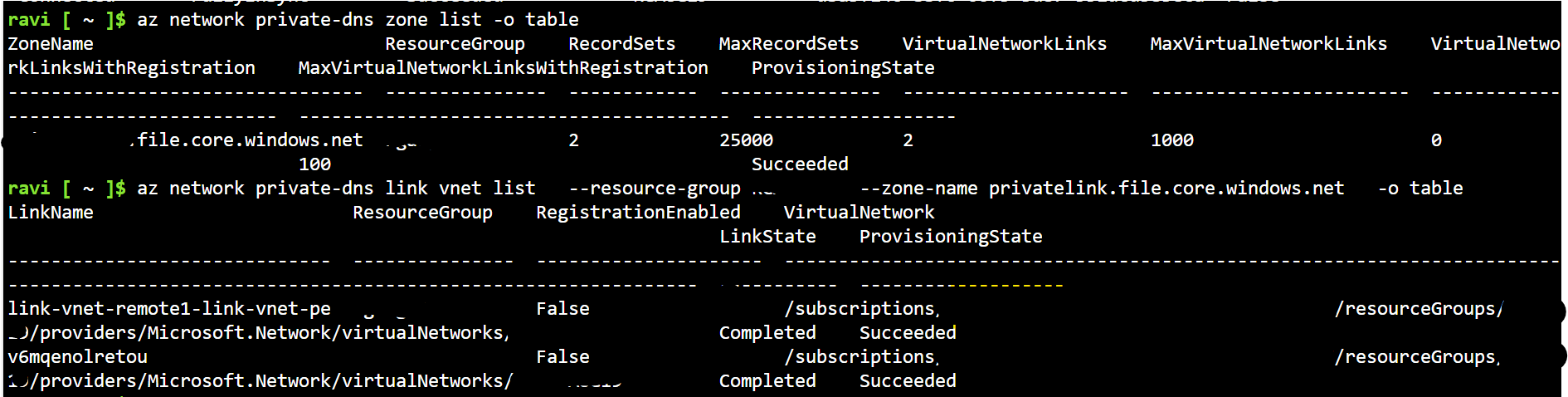
- Please verify the DNS zone links.
az network private-dns zone list -o table
Locate your privatelink.file.core.windows.net zone, then run:
az network private-dns link vnet list --resource-group <RG_NAME> --zone-name privatelink.file.core.windows.net -o table
Ensure that the failing VM’s VNet is properly linked to the Private DNS zone. Refer to the screenshot below for reference.
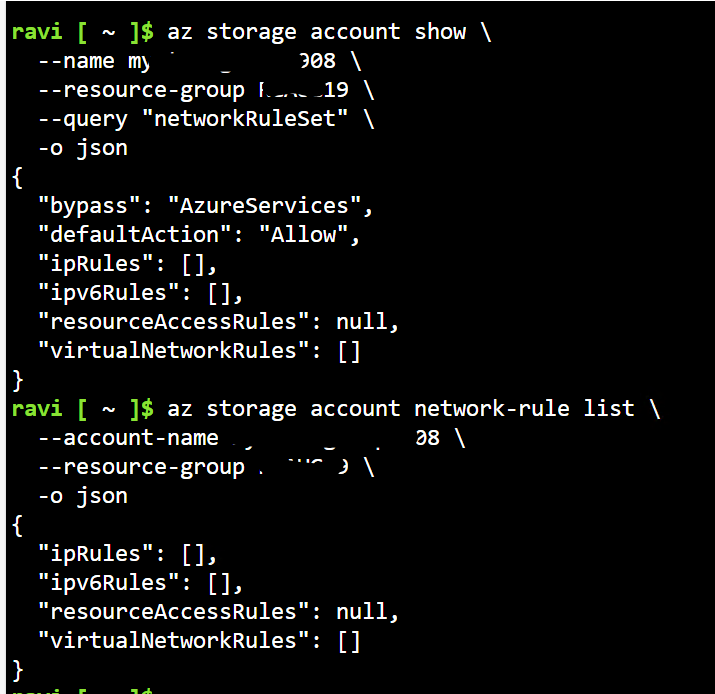
6)Please review the storage account firewall rules.
az storage account network-rule list --account-name <STORAGE_ACCOUNT_NAME> --resource-group <RG_NAME> -o table
az storage account show \ --name mystoragesep1908 \ --resource-group RGAUG19 \ --query "networkRuleSet" \ -o json
Check for:
-
"defaultAction": "Allow" → Storage is accessible from all networks.
-
"defaultAction": "Deny" → Only the VNets/Private Endpoints listed are allowed.
Important: For a Private Endpoint (PE) scenario, the expected configuration is:
-
defaultAction = Deny
- Network rules must include your Private Endpoint.
- Ensure the VNet/subnet with your Private Endpoint is listed.
In my setup, I allowed all networks, so I see an empty list ([]).
Please follow the steps below for the target VM (PE’s Subnet/VNet).
Since I haven’t created a route table, I’m only providing the command:
1.Check PE Subnet Network Policy
- You already confirmed that Private endpoint network policy = Disabled.
- No further changes are required here.
- Verify the subnet’s route table using:
az network route-table show --name <ROUTE_TABLE_NAME> --resource-group <RG_NAME> -o table
Ensure that no UDR is redirecting 0.0.0.0/0 or 10.0.0.0/8 to a firewall or NVA.
3.Please check the VNet peering from PE VNet to Client VNet:
az network vnet peering list \ --resource-group <PE_RG> \ --vnet-name <PE_VNET_NAME> \ -o table
It must show "allowVirtualNetworkAccess": true (as noted in Step 4).
If you run all the above commands for both the working VM and the failing VM. Compare the results side by side.
If you find differences in the Effective Routes or DNS zone links, that is causing the issue
If the Client VM resolves to the PE private IP but port 445 fails: DNS is working correctly and the issue lies with Routing, NSG, or Peering
Kindly let us know if the above helps or you need further assistance on this issue.
If the answer is helpful, please click "Accept Answer" and kindly upvote it. If you have extra questions about this answer, please click "Comment".
