Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Azure Data Explorer uses role-based access control (RBAC) to manage who can access cluster resources. This security model maps principals—such as users, groups, and applications—to specific security roles that determine their level of access.
Use cluster-level permissions to control access across all databases in your cluster. You can assign three types of cluster roles: AllDatabasesAdmin for full administrative access, AllDatabasesViewer for read-only access to all data and metadata, and AllDatabasesMonitor for monitoring capabilities.
This article shows you how to assign cluster-level permissions to principals using the Azure portal.
Note
- To configure cluster level permissions with C#, Python, and ARM templates, see Add cluster principals.
- To configure cluster level permissions with the Azure CLI, see az kusto.
Cluster level permissions
| Role | Permissions |
|---|---|
AllDatabasesAdmin |
Full access in the scope of any database. Might show and alter certain cluster-level policies. Includes all lower level All Databases permissions. |
AllDatabasesViewer |
Read all data and metadata of any database. |
AllDatabasesMonitor |
Execute .show commands in the context of any database and its child entities. |
Manage cluster permissions in the Azure portal
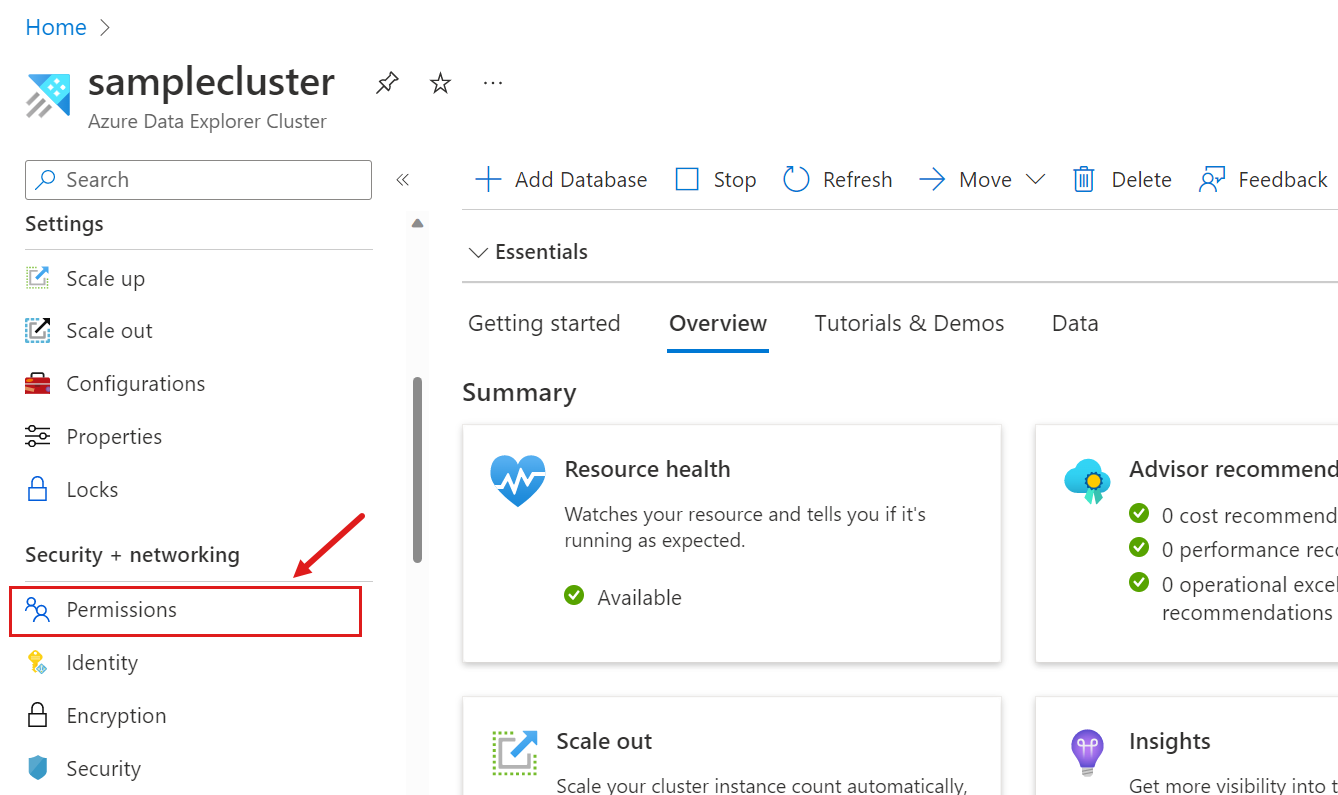
Sign in to the Azure portal.
Go to your Azure Data Explorer cluster.
In the left-hand menu, under Security + networking, select Permissions.
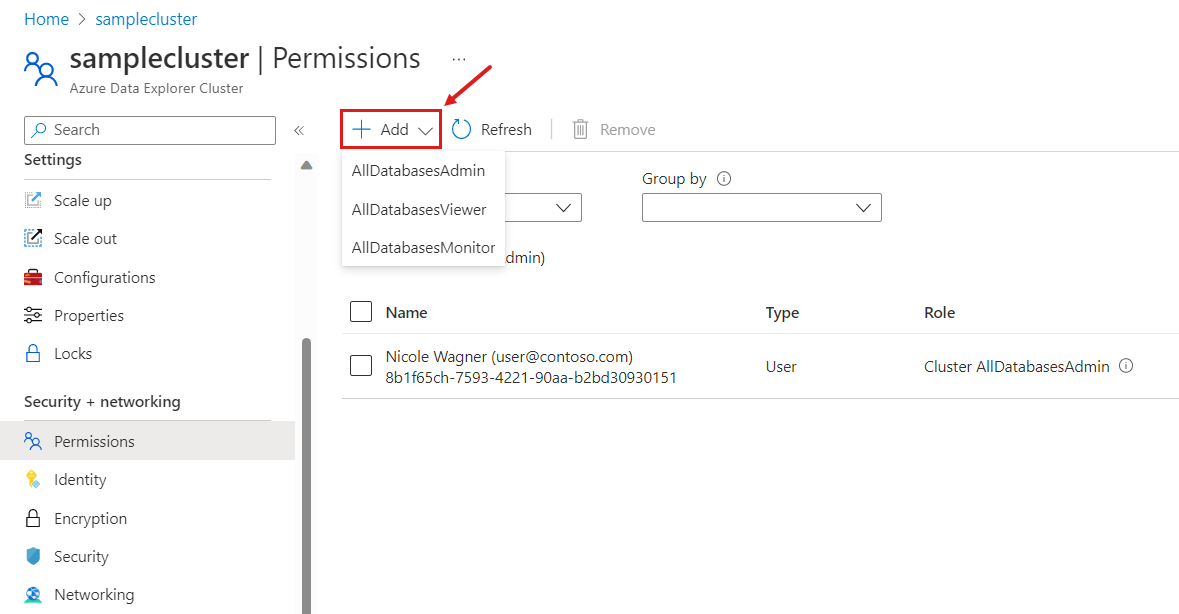
Select Add, and select the role you want to assign.
In the New principals window, search for and select one or more principals.
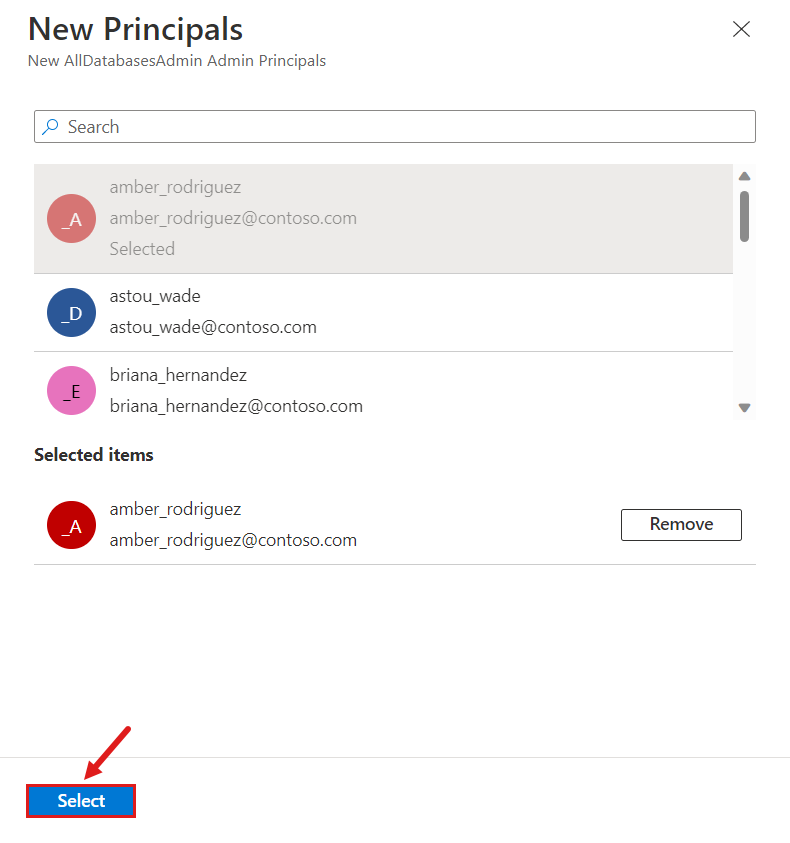
Select Select to complete the assignment.