Note
Access to this page requires authorization. You can try signing in or changing directories.
Access to this page requires authorization. You can try changing directories.
Azure DevOps Services | Azure DevOps Server 2022 | Azure DevOps Server 2020
This article explains how to manage permissions and access by using security groups. You can use default or custom groups to set permissions. You can add users and groups to multiple groups. For instance, you add most developers to the Contributors group. When they join a team, they also join the team’s group.
For more information, see the following articles:
- Add an Active Directory / Microsoft Entra group to a built-in security group
- Add organization users and manage access
- Add users or groups to a team or project
- Remove user accounts
- Manage access to specific features using permissions
- Change project-level permissions
- Change permissions at the organization or collection-level
Users inherit permissions from the groups that they belong to. If a permission is set to Allow for one group and Deny for another group to which the user belongs, then their effective permission assignment is Deny. To learn more about inheritance, see About permissions and security groups.
How Azure DevOps uses security groups
Azure DevOps uses security groups for the following purposes:
- Determine permissions allocated to a group or user
- Determine access level allocated to a group or user
- Filter work item queries based on membership within a group
- Use
@mentionof a project-level group to send email notifications to members of that group - Send team notifications to members of a team group
- Add a group to a role-based permission
- Set object-level permissions to a security group
Note
Security groups are managed at the organization level, even if they are used for specific projects. Depending on user permissions, some groups might be hidden in the web portal. To view all group names within an organization, you can use the Azure DevOps CLI tool or our REST APIs. For more information, see Add and manage security groups.
Note
Security groups are managed at the collection level, even if they are used for specific projects. Depending on user permissions, some groups might be hidden in the web portal. To view all group names within a collection, you can use the Azure DevOps CLI tool or our REST APIs. For more information, see Add and manage security groups.
Prerequisites
| Category | Requirements |
|---|---|
| Permissions | - To manage permissions or groups at the project level: Member of the Project Administrators security group. - To manage permissions or groups at the collection level: Member of the Project Collection Administrators group. Organization owners are automatically members of this group. |
Note
Users added to the Project-Scoped Users group can't access most Organization settings pages, including permissions. For more information, see Limit user visibility.
Create a custom security group
Create a project-level group when you want to manage permissions at the project or object level for a project. Create a collection-level group when you want to manage permissions at the collection level. For more information, see Change project-level permissions and Change permissions at the organization or collection-level.
Create a project-level group
Open the Azure DevOps web portal, and select the project where you want to add users or groups. To choose another project, see Switch project, repository, team.
Select Project settings > Permissions.

Select New Group to open the dialog for adding a group.
Create a project collection-level group
Open the web portal and select the
 Azure DevOps icon, and then select
Azure DevOps icon, and then select  Organization settings.
Organization settings.
Under Security, select Permissions, and then choose New group to open the dialog for adding a group.

Define the new group
In the dialog that opens, enter a Name for the group. Optionally, add members and a description for the group.
For example, here we define a Work Tracking Administrators group.

Choose Create when you're done.
Open the Azure DevOps web portal, and select the project where you want to add users or groups. To choose another project, see Switch project, repository, team.
Select Project settings > Security.
To see the full image, select to expand.
Under Groups, choose one of the following options:
- Readers: To add users who require read-only access to the project.
- Contributors: To add users who contribute fully to this project or who were granted Stakeholder access.
- Project Administrators: To add users who need to administrate the project. For more information, see Change project-level permissions.
Select the Members tab.
Here we choose the Contributors group.

The default team group, and any other teams you add to the project, get included as members of the Contributors group. Add a new user as a member of a team instead, and the user automatically inherits Contributor permissions.
Tip
Managing users is much easier using groups, not individual users.
Choose
 Add to add a user or a user group.
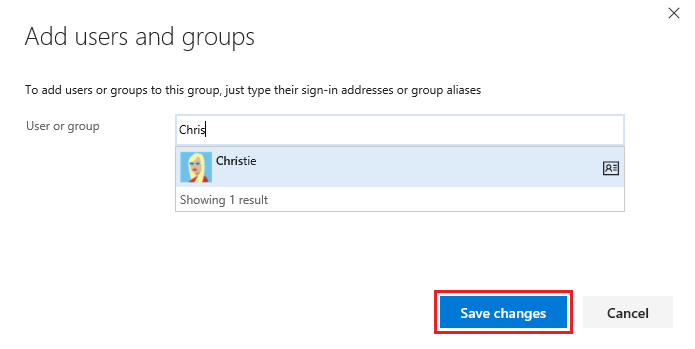
Add to add a user or a user group.Enter the name of the user account into the text box. You can enter several identities into the text box, separated by commas. The system automatically searches for matches. Choose the matches that meet your requirements.
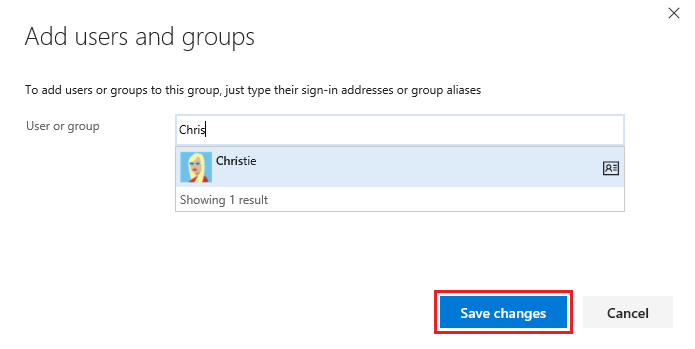
The first time you add a user or group to Azure DevOps, you can't browse to it or check the friendly name. After the identity gets added, you can just enter the friendly name.
Choose Save changes when you're done.
(Optional) You can customize a user's permission for other functionality in the project. For example, in areas and iterations or shared queries.
Note
Users with limited access, such as Stakeholders, can't access select features even if granted permissions to those features. For more information, see Permissions and access.
Add users or groups to a security group
As roles and responsibilities change, you might need to change the permission levels for individual members of a project. The easiest way to do that is to add the user or a group of users to either a default or custom security group. If roles change, you can then remove the user from a group.
The following steps show how to add a user to the built-in Project Administrators group. The method is similar no matter what group you're adding. If your organization is connected to Microsoft Entra ID or Active Directory, then you can add security groups defined in those directories to Azure DevOps security groups. For more information, see Add Active Directory / Microsoft Entra users or groups to a built-in security group.
If you need to add more than 10k users or groups to an Azure DevOps security group, we recommend adding an Azure Directory / Microsoft Entra group containing the users, instead of adding the users directly.
Open the Permissions page for either the project-level or organization-level as described in the previous section, Create a custom security group.
Choose the security group whose members you want to manage, then choose the Members tab, and then choose Add.
For example, here we choose the Project Administrators group, Members, and then Add.

Enter the name of the user account into the text box and then select from the match that appears. You can enter several identities recognized by the system into the Add users and/or groups box. The system automatically searches for matches. Choose the matches that meet your choices.

Note
Users with limited access, such as Stakeholders, can't access select features even if granted permissions to those features. For more information, see Permissions and access.
Select Save.
Open the Permissions page for either the project-level or organization-level as described in the previous section, Create a custom security group.
Choose the security group whose members you want to manage, then choose the Members tab, and then choose Add.
For example, here we choose the Project Administrators group, Members, and then Add.

Enter the name of the user account into the text box. You can enter several identities into the text box, separated by commas. The system automatically searches for matches. Choose the matches that meet your choice.
Note
Users with limited access, such as Stakeholders, can't access select features even if granted permissions to those features. For more information, see Permissions and access.
Choose Save changes. Choose the
 refresh icon to see the additions.
refresh icon to see the additions.
Change permissions for a user or group
Because permissions are defined at different levels, review the following articles to open the dialog for the permissions you want to change:
Remove users or groups from a security group
For the user or group you want to remove, select
 the vertical ellipses, then choose Remove.
the vertical ellipses, then choose Remove.
Select Delete to confirm removal of the group member.

To remove a user from a group, choose Remove next to the user's name that you want to remove.

Manage group settings
Open the Permissions page for either the project-level or organization-level as described earlier in this article, Create a custom security group.
Choose the Settings tab. You can change a group description, add a group image, or delete a group through the group Settings page.
From the Project settings > Permissions or Organization settings > Permissions page, choose the group you want to manage, and then choose Settings.
For example, here we open the Settings for the Work Tracking Administrators group.

You can modify the group name, group description, upload an image, or delete the group.
You can change a group name, description, add a group image, or delete a group.
From the Project > Settings > Security or Organization page, choose the group you want to manage
Choose from the Edit menu to either Edit profile or Delete.
For example, here we open the Edit profile for the Stakeholder Access group.

Change the description. You can change the name of the group as well.

Choose Save to save your changes.
On-premises deployments
For on-premises deployments, see these other articles:
If your on-premises deployment is integrated with SQL Server Reports, you need to manage membership for those products separately from their websites. To learn more, see Grant permissions to view or create SQL Server reports in Azure DevOps Server.
