Current landscape of K-12 cybersecurity
In this unit, you learn about the current K-12 cybersecurity landscape and are introduced to how you, as an educator, can prepare to implement cybersecurity measures in your classroom.
Cyberattacks on K-12 schools have become a serious concern in recent years, as the education sector increasingly relies on digital technology to support teaching and learning activities. With the widespread adoption of online learning platforms, student information systems, and other digital tools, schools are a rich target for cybercriminals looking to exploit vulnerabilities in these systems.
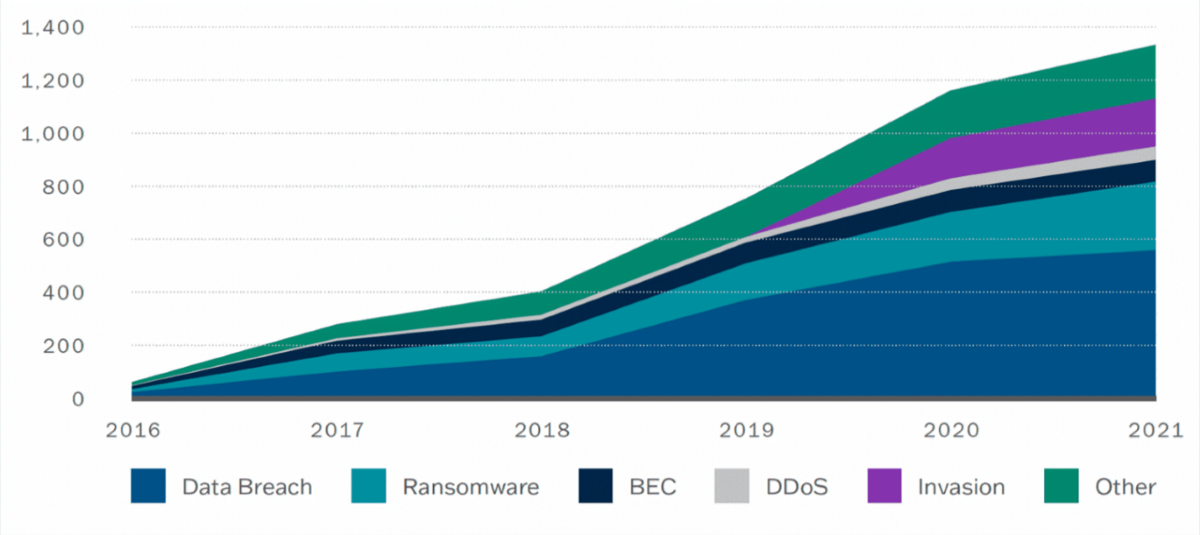
Moreover, schools are often seen as easier targets for cybercriminals when compared to other organizations, as they might have limited resources and technical expertise to secure their networks adequately. Cumulative reported incidents over the past five years show a significant increase in school-focused attacks. Since 2016, the K12 Security Information eXchange cataloged over 1,619 incidents, a rate of more than one incident per school day. These attacks disrupt daily operations, compromise sensitive data, and in some cases, even endanger students and staff.
How schools are responding
As cyber threats and incidents continue to rise, schools must respond swiftly with cybersecurity measures to mitigate the potential effects of an attack. Cybersecurity involves protecting the data, systems, and operations that make learning with technology possible in K-12 schools.
Robust cybersecurity measures include:
- Steps for detecting, preventing, and responding to threats.
- Institutional participation and awareness from the youngest student all the way to educators, administrators, and IT professionals.
- Security technologies that detect, protect, and respond to incoming threats.
This video and list provide an overview of recommended practices to mitigate cyber threats in schools.
- User authentication: Strong user authentication methods, like multifactor authentication (MFA) and two-factor authentication (2FA), help ensure that only authorized users access school systems.
- Data encryption: Software that encrypts sensitive data helps safeguard student records and other confidential information.
- Content filters: Use of content filters restricts access to inappropriate or potentially harmful websites.
- Firewalls: Firewalls monitor and filter network traffic to detect and prevent unauthorized access or cyberattacks.
- Backups: Regular backups ensure that critical data can be restored after a cyber incident or data breach.
- Security awareness training: Regular training for students on cybersecurity best practices helps mitigate human error.
- Incident response plans: Schools should have a well-defined incident response plan in place to address cyber incidents promptly and effectively.
- Regular updates and patch management: Keeping software and devices up to date with the latest security patches is essential to plug vulnerabilities.
The role of educators in cybersecurity
Shared accountability and responsibility—including active participation from students, educators, and administrators—are essential elements to ensuring secure digital learning experiences. When it comes to cybersecurity in the classroom, what’s required is an ability to:
- Recognize potential threats.
- Respond appropriately.
- Maintain security defenses.
But what if you don’t know how to recognize cyber threats or what to do when an incident occurs? It’s difficult to play your part if you don’t fully understand the issue at hand. Just like eliminating fire hazards and practicing fire drills create a safer school, understanding practical cybersecurity measures and how to respond prevents disruptions from becoming major issues that impact the school community.
K-12 cybersecurity recommendations
In collaboration between the Cybersecurity and Infrastructure Security Agency (CISA) and education industry stakeholders, the Protecting Our Future report, released in January 2023, provides context for the cyber risks that schools face as well as recommendations that schools should follow.

Among the data and results from the study, CISA published several key findings and recommendations that you'll review throughout this module to safeguard K-12 organizations from cybersecurity threats:
Key finding 1: K-12 institutions can take a small number of steps to have a large impact on reducing cybersecurity risk. Leaders should invest in security measures with the greatest impact and build toward a mature cybersecurity plan.
Key goals:
- Implement multifactor authentication (MFA).
- Prioritize patch management.
- Perform and test back-ups.
- Minimize exposure to common attacks. Develop and exercise an incident response plan.
- Create a training and awareness campaign at all levels.
Key finding 2: Many districts struggle with insufficient resources and cybersecurity capacity. Leaders should identify resource constraints and take creative approaches to secure the necessary funding and services.
Key goals:
- Partner with state organizations.
- Seek and apply for cybersecurity grants.
- Use free or low-cost tools and services.
- Demand higher security controls from technology providers.
- Migrate IT services to the cloud.
Key finding 3: No K-12 entity can single-handedly address cybersecurity on their own. Information sharing and collaboration with partners is essential to build awareness and sustain resilience.
Key goals:
- Participate in state, regional, or national cybersecurity discussions.
- Join communities and forums to share experiences.
- Share information with CISA and the FBI.
Next steps
- Explore cyber incidents in your local region using K12 Six’s interactive Cyber Incident Map.
- Pause and reflect on your current understanding of cybersecurity. Note any areas you’d like to focus on throughout this module:
- Understanding current cybersecurity threats in schools and knowing how to spot them
- Recognizing common ways that cyber attackers target schools and classrooms
- Knowing how to protect classroom devices from cyberattacks
- Knowing how to keep data and student information private
- Knowing what to do if a cyberattack occurs
- Having the right resources to educate students about cybersecurity